Compliance proven.
Because your security is
continuously generating it.
PacketViper generates continuous, tamper-evident audit trails as a byproduct of enforcement – so audit prep isn’t a scramble, it’s a query.
Good security produces compliance evidence automatically. Bad security produces audit panic.
Two weeks before the audit. Urgent requests to six different teams.
Two weeks before an audit, a compliance team sends urgent requests to security, networking, IT operations, and three separate vendors – trying to reconstruct evidence of controls that should have been running continuously for the past twelve months.
Most organizations treat compliance as a separate workstream: implement controls for the audit, document the controls for the audit, generate reports for the audit. Then go back to running security normally until the next audit.
Regulators don’t accept reconstructed evidence the way they used to. NIST, IEC 62443, PCI DSS, ISO 27001 – frameworks are increasingly specific about continuous monitoring, continuous logging, and tamper-evident trails.
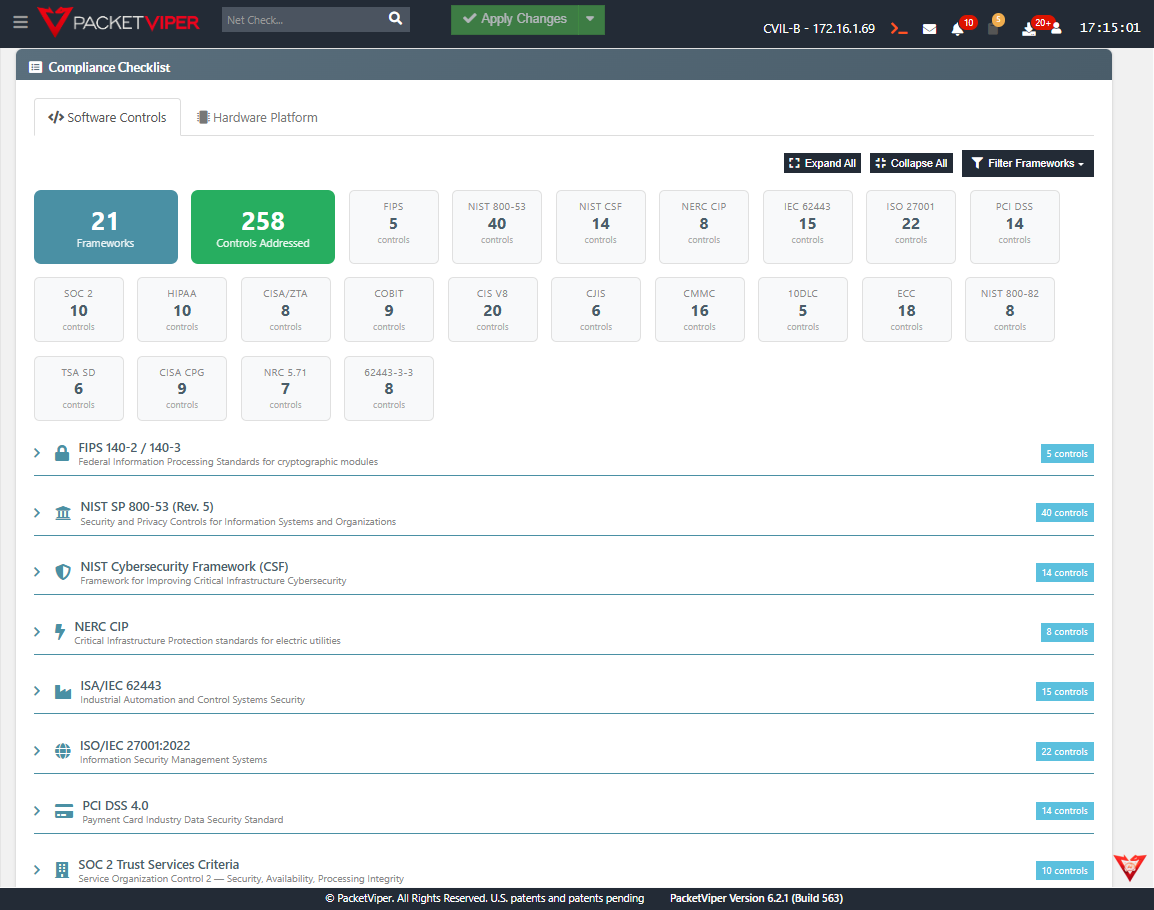
Map your compliance requirement to what PacketViper already generates.
Click any framework to see the specific controls PacketViper addresses.
Evidence generated automatically. Not reconstructed at audit time.
Continuous Tamper-Evident Logging
Every enforcement action, every policy change, every access event, every detected anomaly writes to a tamper-evident, time-stamped log – not because compliance requires it, but because that’s how the platform operates.
Real-Time Security Posture
Current compliance state against configured frameworks in real time. Not point-in-time snapshots. Not quarterly assessments. Current, live, queryable.
Compliance Checklist Mapping
Platform activities mapped to framework requirements. When an auditor asks for evidence of continuous monitoring from the past 90 days, the answer is a query and an export – not a two-week reconstruction project.
Change Audit Trail
Every configuration change captured – who made it, what changed, when, from what state to what state. Tamper-evident and available for auditor review without special preparation.
User Activity Audit
All administrative actions in the platform captured and attributable. Not just what changed – who changed it and when.
Scheduled Posture Reports
Regular delivery to leadership and compliance teams without manual preparation. Compliance posture is never a surprise.
Continuous compliance. Not audit-season compliance.
For Security Teams
Stop running the pre-audit evidence sprint. The data is there. It’s always been there. It’s queryable in seconds.
For OT Operators
IEC 62443 compliance for industrial control systems – evidence generated by the security layer that’s already running, not a separate compliance tool.
For Leadership
Audit prep time drops dramatically when the evidence is continuous rather than reconstructed. Compliance risk drops when posture is visible in real time, not quarterly.
See what your firewall never told you.
Book a live demo – we’ll show you in your environment, not ours.
PacketViper's inline monitoring and Deceptive Responders align with NERC CIP-015-1 Internal Network Security Monitoring requirements. The platform provides forensic-level logging, automated audit trails, change audit history, and evidence-ready compliance reporting for electric utility environments.
PacketViper supports NERC CIP, ISA/IEC 62443, NIST CSF 2.0, CISA Zero Trust Maturity Model, ISO/IEC 27001, SOC 2, and PCI DSS. Its compensating control capabilities are particularly valuable for legacy OT environments where primary security controls cannot be applied to aging industrial devices.
A compensating control is an alternative security measure that satisfies a compliance requirement when the primary control cannot be applied. PacketViper serves as a compensating control for organizations with legacy OT devices that cannot be patched or directly secured – enforcing network-layer protection without modifying the devices themselves.