Water treatment doesn’t get a
maintenance window.
Security can’t need one either.
PacketViper protects water and wastewater OT environments with passive, agentless security that can’t interrupt treatment operations – while detecting and containing threats that could compromise public health.
The Oldsmar attack took 30 seconds. The damage could have taken weeks to reverse.
The Problem
30 seconds of remote access. A public health crisis nearly happened.
Water and wastewater OT environments face a specific challenge: equipment is fragile, software is legacy, uptime requirements are absolute, and the consequences of a breach are severe. Public health, service disruption, regulatory violation.
You can’t patch a 15-year-old SCADA controller. You can’t install an agent on a PLC that’s been running without interruption for a decade. You can’t afford to disrupt treatment to run a security scan.
Remote Access Left Wide Open
The Oldsmar attacker had credentials – likely from a previous breach – and walked through remote access software with no MFA, no geographic controls, and no behavioral monitoring. The session looked normal until sodium hydroxide levels were already climbing.
Legacy OT That Can’t Accept Security Tools
Water treatment controllers, PLCs, and SCADA systems were built to run for decades without interruption – not to run antivirus or accept agent-based security. Any security approach that requires touching these systems is an approach that can’t be deployed.
Chemical Dosing Anomalies With No Enforcement
Treatment parameter commands – chemical dosing levels, pump speeds, valve positions – traverse SCADA networks with no protocol-level enforcement. A Modbus command that would push a parameter to a dangerous level looks identical to a normal operational command until a human happens to notice it.
How It Works
Inline enforcement that fires before an operator notices the mouse moving
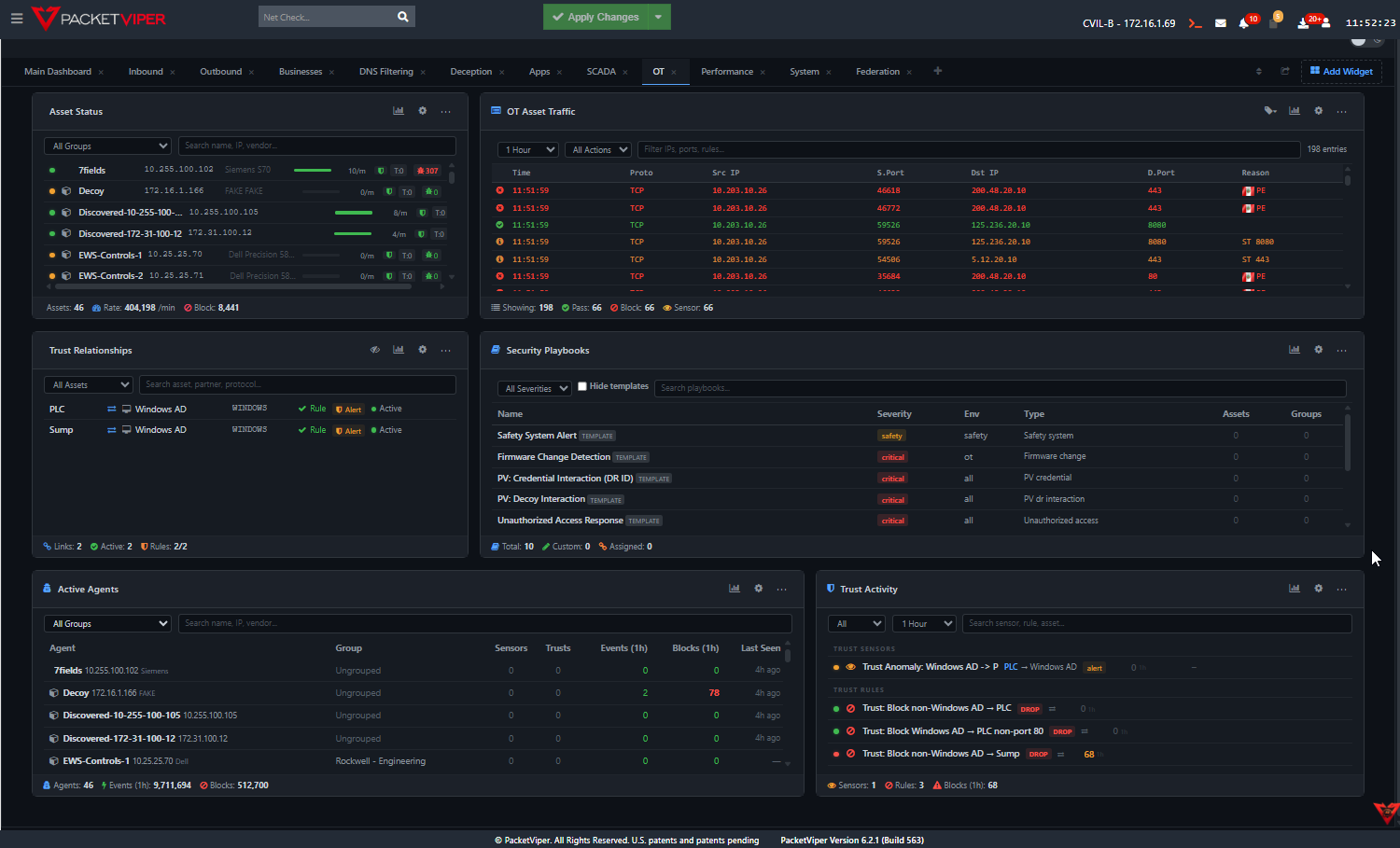
PacketViper deploys as a transparent bridge on the water/wastewater OT network. No changes to SCADA systems, no agents on controllers, no active scanning. The inline path sees all traffic between IT and OT, between control systems, between HMIs and PLCs.
Treatment operations continue without interruption. The security layer is invisible to every controller and sensor it protects.
SCADA and Modbus Protocol Enforcement
PacketViper understands what normal chemical dosing commands look like versus outlier command sequences. A command that would push a treatment parameter far outside normal operational bounds – like pushing sodium hydroxide from 111 ppm to 11,100 ppm – triggers inline enforcement immediately, not after a human reviews a log.
Remote Access Geographic & Behavioral Controls
Vendor sessions are allowed from expected source geography during expected time windows. Any session from an unexpected location or outside expected windows gets flagged and can be blocked automatically. The Oldsmar attack vector – a remote session from an unexpected source – would have been blocked at the session level before a single command reached the SCADA system.
AMTD – Deceptive SCADA & HMI Infrastructure
Attackers who probe the OT network encounter fake SCADA systems and HMI interfaces that look real, capturing their fingerprints and burning their reconnaissance time before they reach actual treatment controls. Decoys are indistinguishable from production systems to attacker tooling.
SCADA Integration – Alerts in the Operator Console
Security events surface directly into the water management SCADA console via Modbus – operators see security alerts in the same interface they use to monitor treatment parameters. No separate security dashboard to learn. No context-switching. The alert appears where the operator is already looking.
Autonomous RSU Enforcement – Operates Without WAN
Remote water facilities continue enforcing security policy without internet connectivity. The RSU operates autonomously when WAN connectivity is interrupted – no cloud dependency, no central management requirement for enforcement to continue at the edge.
Proof Points
What preemptive enforcement means for water/wastewater operators
Water/wastewater OT is a federal critical infrastructure sector with increasing regulatory scrutiny. Coverage needs to match the designation. PacketViper closes the Oldsmar-style attack vector with automated enforcement rather than operator vigilance.
Treatment operations continue without interruption. The security layer is transparent to every controller, sensor, and SCADA system it’s protecting. No configuration changes, no software installs, no maintenance windows.
The Oldsmar incident was a near-miss that made national news. The next one may not be caught by an operator watching a screen. Automated inline enforcement closes that window – and provides documented evidence of continuous monitoring for regulatory requirements.
See what your firewall never told you.
Review your water/wastewater OT security posture with us. We’ll map the gaps against the Oldsmar attack vector and show what preemptive enforcement looks like in your environment.
Water utilities face threats including nation-state actors attempting to manipulate chemical dosing controls, ransomware targeting SCADA systems managing treatment processes, and unauthorized remote access to pump stations and distribution systems. The consequences extend beyond data loss to potential public health impacts, making inline enforcement – not just detection – essential.
PacketViper deploys inline between SCADA and the wider network, providing Modbus-native protocol awareness to distinguish legitimate engineering commands from malicious manipulation attempts. Deceptive Responders emulate PLCs and SCADA interfaces to detect unauthorized access, while the Hive architecture ensures threats detected at any site are blocked across the entire water authority network.
Yes. PacketViper's RSU is specifically designed for unmanned remote sites – ruggedized, fanless, industrial-grade, and capable of fully autonomous operation. It detects threats, enforces containment, alerts via SCADA Modbus polling (so operators see alerts in their existing DCS), and propagates blocks enterprise-wide – all without requiring anyone to be on site.