Attackers can’t hit what keeps moving.
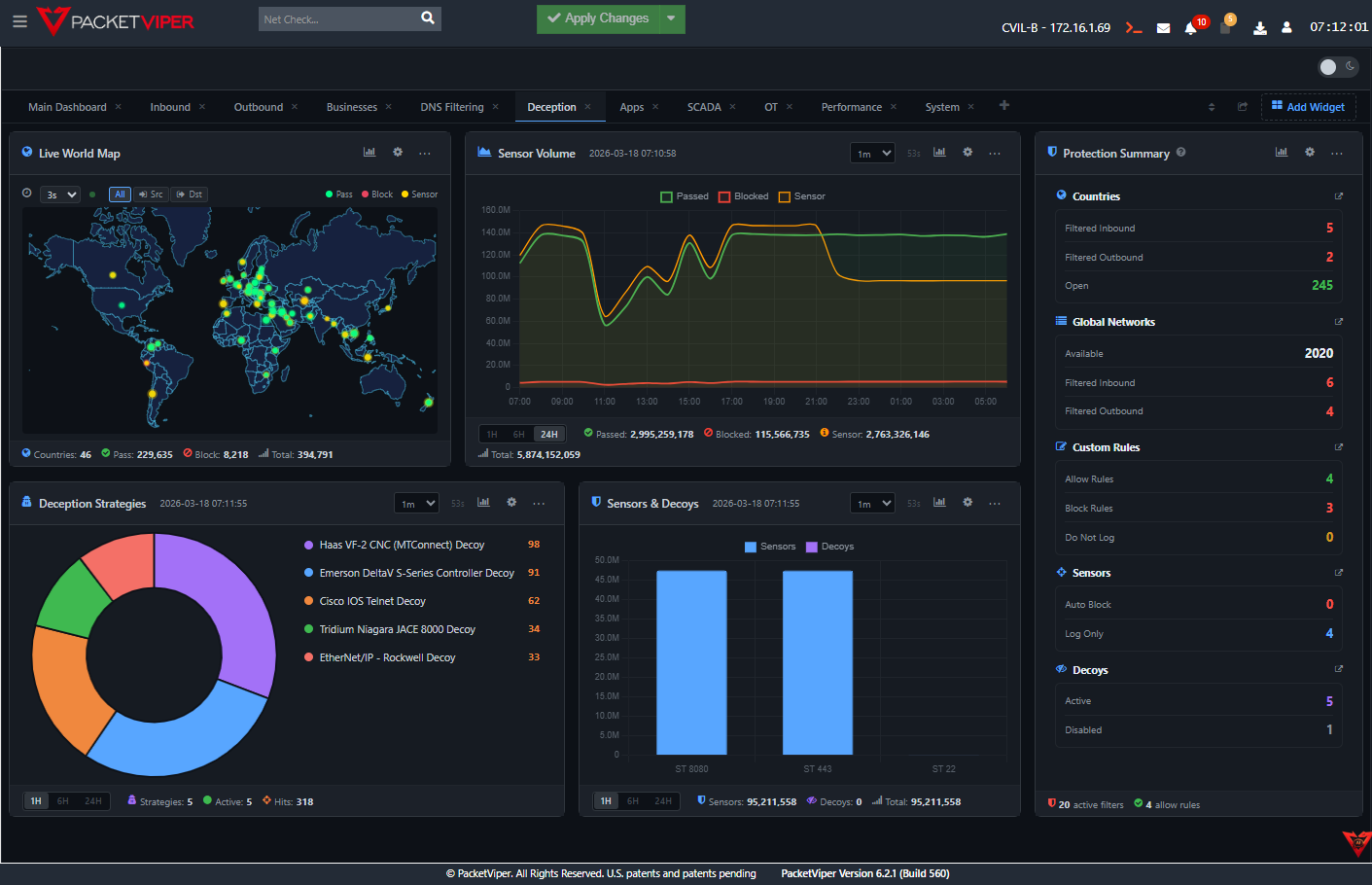
PacketViper’s AMTD continuously morphs your attack surface – hundreds of sensors, always rotating – so every scan costs the attacker and every probe generates signal for you.
Static defenses are known quantities. Dynamic ones are minefields.
Your network is a map.
Attackers have a copy.
Traditional security assumes a static environment – defined IPs, fixed services, predictable behavior. Attackers exploit exactly that predictability. Before they strike, they spend hours – sometimes days – mapping your infrastructure, cataloging every service, fingerprinting every device.
By the time a threat appears in your SIEM, the reconnaissance is complete. The attacker already knows more about your network than most of your own team does. Every perimeter rule, every ACL, every asset – cataloged, weaponized, waiting.
“A security tool that can be mapped is a tool that can be beaten.”
Deception-based defenses flip this model. Instead of hardening a static surface, PacketViper makes your surface a moving target – so every scan gets different results, every probe hits a sensor, and every fingerprint goes stale.
The five-step loop that never stops.
AMTD isn’t a one-time configuration – it’s a continuous loop that runs autonomously. The surface rotates, the decoys respond, and every attacker interaction becomes intelligence. Here’s what happens from first probe to fingerprint.
No manual tuning. No alert fatigue. No human-in-the-loop required for enforcement – only for the insights that matter.
Attacker begins reconnaissance
Port scans, banner grabs, SNMP walks – the attacker starts mapping. On a conventional network, this works exactly as expected.
Sensors detect the probe
PacketViper’s distributed sensors – deployed across every segment – detect the probe instantly. Attribution begins: source, timing, method, intent pattern.
AMTD rotates the surface
The visible network surface shifts – IPs, ports, banners, service signatures. What the attacker just mapped is already wrong. The next scan will return different results.
Probe hits decoy – inline enforcement fires
The attacker follows their map to what looks like a real asset. It’s a decoy. The moment they interact, inline enforcement engages – block, throttle, redirect, or capture, depending on your policy.
Mapping failed and they’ve been fingerprinted.
Every probe, connection attempt, and decoy interaction builds a persistent attacker profile. The attacker wasted hours. You have a complete behavioral fingerprint, enriched with context, ready for your SOC.
Every layer of your defense, reinvented.
AMTD isn’t a single technique – it’s a platform capability that touches every part of your network posture.
Dynamic Surface Rotation
Continuously randomizes IP addresses, open ports, service banners, and protocol responses – making every network scan a new experience for the attacker.
Deception Grid Deployment
Hundreds of convincing decoy assets – fake services, emulated devices, honey credentials – distributed across your real network to attract and trap adversaries.
Attacker Fingerprinting
Every probe contributes to a persistent attacker profile: TTL values, scan patterns, tooling signatures, timing, and behavioral indicators of intent.
Inline Enforcement
Enforcement runs in the packet path – no cloud dependency, no agent, no latency. Block, redirect, throttle, or tarpit attackers in microseconds.
Segmentation Enforcement
AMTD-driven segmentation policies that adapt based on observed behavior – not static rules. Attackers who probe east-west traffic get progressively isolated.
Automated Countermeasures
When an attacker hits a deception trigger, automated infrastructure depletion begins – consuming their time, tools, and resources without human intervention.
Automated Infrastructure Depletion
When an attacker engages with PacketViper’s deception layer, they don’t just get blocked – they get consumed. Automated Infrastructure Depletion (AID) responds to attacker interaction by feeding plausible-but-false data, stalling connection handshakes, and forcing the attacker to exhaust their tooling against an environment that doesn’t exist.
The result: every minute an attacker spends in your deception grid is a minute they’re not in your real network. And they’re generating signal the entire time. Their tools burn cycles. Their timelines slip. Their operations degrade – automatically, without a single analyst response required.
AMTD in production. These are the real numbers.
Measured across production deployments – not lab benchmarks.
See what your firewall never told you.
Book a live demo – we’ll show you in your environment, not ours.
AMTD continuously shifts network characteristics – IP addresses, service configurations, and access points – to deny attackers a stable surface to map and exploit. PacketViper's patented network-layer AMTD protects both IT and OT environments without requiring changes to the devices being protected.
Deception technology detects attackers post-ingress – it waits for them inside. AMTD operates pre-ingress: it continuously changes the network parameters attackers need for reconnaissance, making planning efforts futile before they reach a decision point. PacketViper uses both in an integrated architecture.
Deceptive Responders simulate realistic network services – SSH, RDP, SCADA, PLCs, Active Directory portals – embedded directly in the PacketViper appliance. When an attacker engages one, PacketViper immediately blacklists the source and propagates that block enterprise-wide through the CMU. No firewall integration or SOAR required.
Yes. PacketViper's AMTD applies changes at the network enforcement layer, not at the device level. PLCs, RTUs, HMIs, and SCADA systems experience zero configuration changes. Native support for Modbus, DNP3, BACnet, and S7COMM ensures enforcement decisions never block legitimate engineering communications.
At wire speed – the local unit immediately creates a blacklist rule, blocks the source, and notifies the CMU, which propagates the rule to all enterprise units. This happens in milliseconds, without human intervention, without a SOAR playbook, and without external enforcement tools.
AMTD continuously shifts network characteristics – IP addresses, service configurations, and access points – to deny attackers a stable surface to map and exploit. PacketViper's patented network-layer AMTD protects both IT and OT environments without requiring changes to the devices being protected.
Deception technology detects attackers post-ingress. AMTD operates pre-ingress: it continuously changes network parameters attackers need for reconnaissance, making planning efforts futile before they reach a decision point. PacketViper uses both in an integrated architecture.
Deceptive Responders simulate realistic services – SSH, RDP, SCADA, PLCs, Active Directory portals – embedded in the PacketViper appliance. When an attacker engages one, PacketViper immediately blacklists the source and propagates the block enterprise-wide through the CMU. No SOAR required.
Yes. PacketViper's AMTD applies changes at the network enforcement layer, not at the device level. PLCs, RTUs, HMIs, and SCADA systems experience zero configuration changes. Native Modbus, DNP3, BACnet, and S7COMM support ensures enforcement never blocks legitimate engineering communications.
At wire speed – the local unit immediately creates a blacklist rule, blocks the source, and the CMU propagates the rule to all enterprise units in milliseconds, without human intervention or a SOAR playbook.