Built for OT.
Not adapted from IT.
No agents. No active scanning. No cloud dependency. No operational disruption. Security that works with your environment, not against it.
IT security tools don’t belong in OT environments.
Most cybersecurity was designed for IT: agentable, cloud-connected, update-friendly. OT environments are none of those things – and the wrong tool can be more dangerous than no tool at all.
Legacy Systems You Can’t Touch
PLCs, RTUs, and SCADA systems running decades-old firmware can’t accept agents or patches. Any security tool that requires a software install is a non-starter – full stop.
Downtime Is Not an Option
A security tool that causes a process disruption in a water treatment plant or power substation isn’t a security tool – it’s a liability. Fail-safe operation is mandatory, not optional.
Air-Gap & Connectivity Constraints
Remote sites – pumping stations, substations, field cabinets – often operate with no reliable WAN connectivity. Cloud-dependent security is no security at all when the link drops.
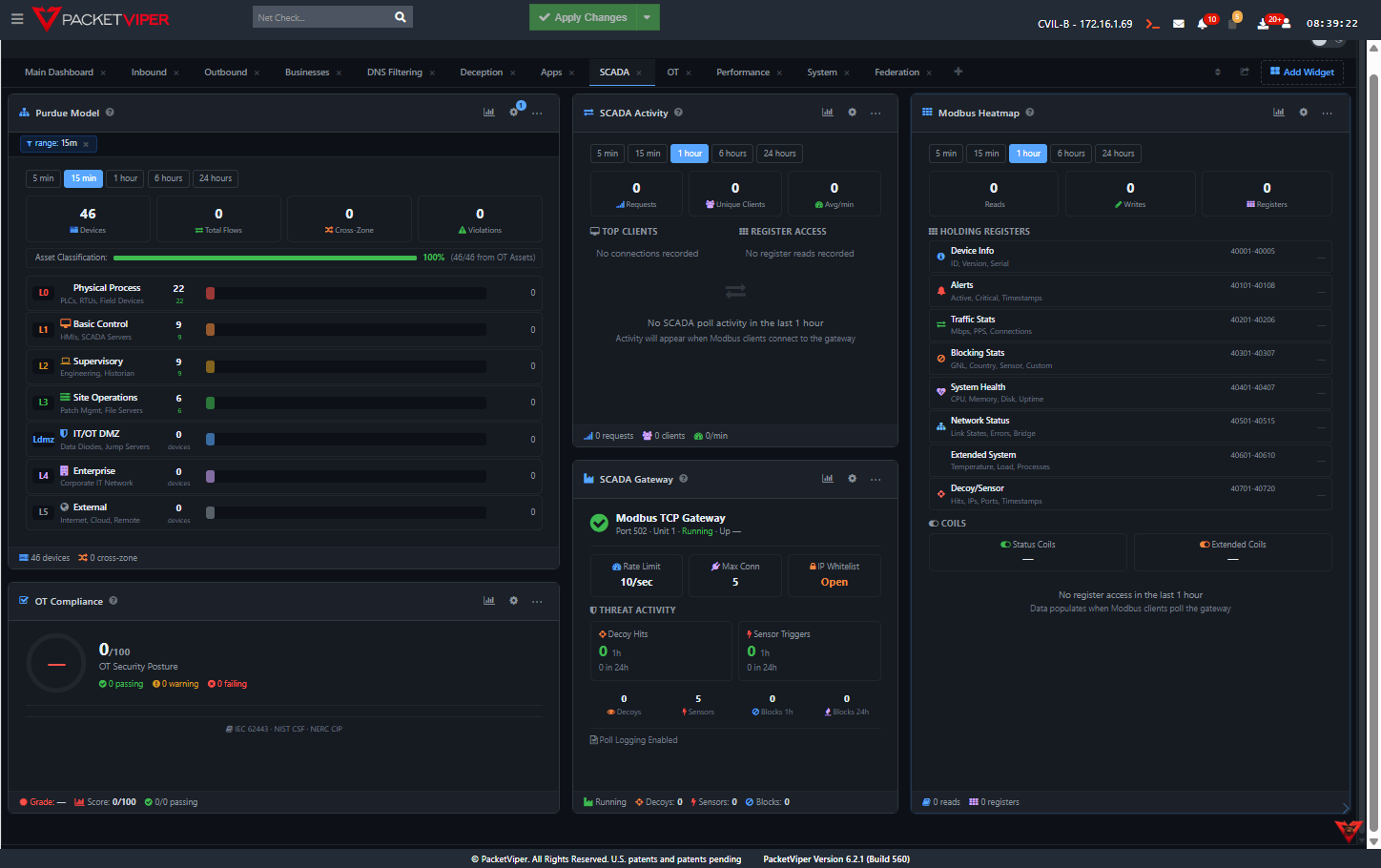
Passive. Protocol-native. Proven.
PacketViper RSUs (Remote Security Units) are compact, ruggedized appliances that install passively in field cabinets – between the switch and the uplink. They see everything. They touch nothing. They enforce silently.
There’s no software to install on your controllers, no cloud dependency for enforcement, and no active scanning that could trip a PLC. Just visibility, intelligence, and inline control where you need it most.
No Agents Required
Passive inline installation – RSUs see all traffic without touching a single endpoint or requiring software on any OT device.
Protocol-Aware Enforcement
Deep packet inspection for OT protocols: Modbus, DNP3, BACnet, S7COMM, NTCIP, EtherNet/IP, IEC 61850, OPC-UA, HART, and Profinet – with field-level command visibility.
Fail-Safe Operation
Hardware bypass mode ensures traffic continues uninterrupted even if the RSU loses power or encounters a fault. Operations never stop because of us.
RSUs in Field Cabinets
DIN-rail mountable, ruggedized enclosures fit standard OT field cabinets. No dedicated rack space, no IT infrastructure required at the remote site.
SCADA Integration via Modbus
Native Modbus integration means your SCADA platform can pull security telemetry directly – no middleware, no custom integration work, no vendor lock-in.
A single RSU protects an entire remote site – substation, pump station, or manufacturing cell. Zero cloud dependency. Autonomous enforcement.